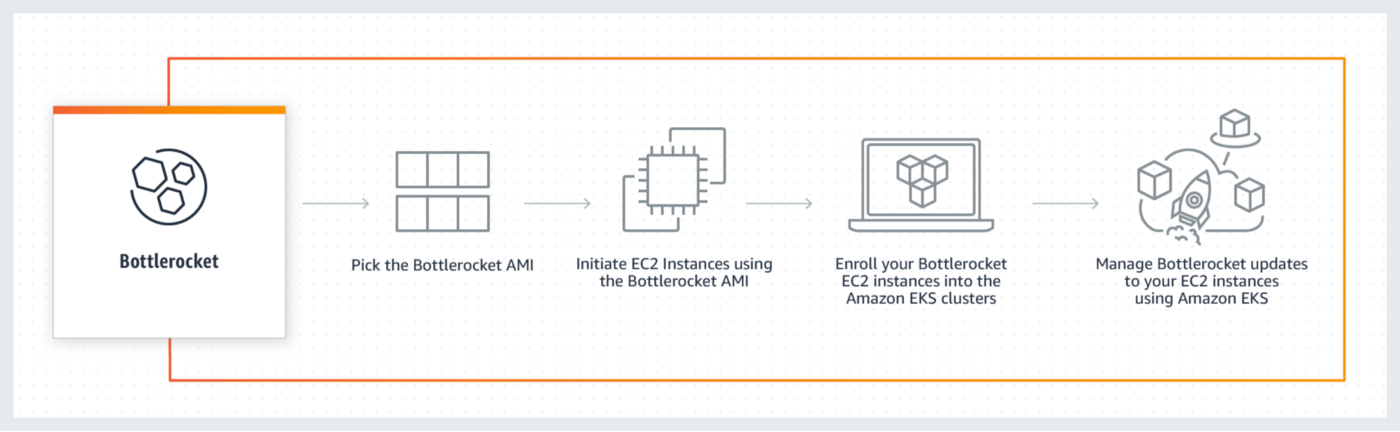
Have containerized workloads on Amazon Web Services? Explore what is AWS Bottlerocket in AWS Elastic Kubernetes Service (EKS) and leverage your security and maintenance to the next level!
Since its release, AWS Bottlerocket has only grown in popularity. Having the most efficient operating system to run containers is easily attainable. Bottlerocket focuses on security and integration with AWS-managed services using containers such as Amazon EKS (Elastic Kubernetes Service) and ECS (Elastic Container Service).
In this article, we will see what is Bottlerocket and its components, and what are the benefits to use it. Then we will create an Amazon EKS cluster with eksctl and explore it.
What Is AWS Bottlerocket
AWS Bottlerocket is an open-source Linux-based OS optimized for running containers on Amazon Web Services. It is inspired by traditional general-purpose Linux distributions as well as some container-focused operating systems like CoreOS Container Linux, RancherOS, and Project Atomic.
It includes only essential software to run containers and comes with a transactional update mechanism. This feature allows users to reduce maintenance requirements, improve security and enhance resource usage. The Bottlerocket's root filesystem is read-only and is backed with dm-verity. It is configured with Security-Enhanced Linux (SELinux) policies for isolation.
A Kubernetes Operator is responsible for updates on hosts in a cluster. When a new Kubernetes node is started in the cluster, the Bottlerocket update operator starts a DaemonSet acting as an agent on this one. The Bottlerocket node is responsible for draining the node, managing periodically querying updates, and performing them when it is required.
AWS Bottlerocket Components
- Bottlerocket manages and orchestrates updates by integration with container orchestrators such as the Amazon EKS service.
- A single-step atomic update mechanism that allows applying and rolling back system updates.
- Minimal components including the Linux Kernel and system software needed for containerization.
- An admin container for advanced troubleshooting and debugging.
Why You Should Use AWS Bottlerocket
- Bottlerocket improves uptime and reduces operational costs. Thousands of OS updates can be applied simultaneously with minimal disruptions to the applications. Rollbacks are automatically done if needed to exclude the risk of errors.
- Bottlerocket improves security and ensures better resource utilization. All the files are read-only and cannot be directly modified by the userspace processes. The integrity of exchanged containers is checked using a cryptographic digest. Any anomaly or corruption can restart the whole process.
- Updates can be easily automated as soon as they are available. Bottlerocket uses image-based updates. AWS claims that the updating process is as simple as updating your phone.
- Bottlerocket is open-source and universally available so anyone interested can make code, design, and dataset changes to it. Users also get everything required due to excellent support by AWS such as Amazon EKR, Amazon EKS, Amazon EC2.
Exploring AWS Bottlerocket on Amazon EKS
Creating the EKS Cluster
Install eksctl :
Here is the YAML file to create the EKS cluster:
---
apiVersion: eksctl.io/v1alpha5
kind: ClusterConfig
metadata:
name: bottlerocket-cluster
region: us-east-1Apply the file to create the cluster:
$ eksctl create cluster -f cluster.ymlDeploying the Bottlerocket EKS node group
Create an SSH key pair to connect to Bottlerocket hosts:
$ aws ec2 create-key-pair \
--key-name my-key-pair \
--key-type rsa \
--query "KeyMaterial" \
--output text > eks_bottlerocket.pemHere is the YAML file to create the Bottlerocket node group:
---
apiVersion: eksctl.io/v1alpha5
kind: ClusterConfig
metadata:
name: bottlerocket-cluster
region: us-east-1
version: 1.20
managedNodeGroups:
- name: bottlerocket-nodegroup
instanceType: t3.medium
minSize: 2
maxSize: 4
desiredCapacity: 2
amiFamily: Bottlerocket
tags:
nodegroup-type: BottlerocketApply the file to create the node group:
$ eksctl create nodegroup --cluster bottlerocket-cluster -f node-group.ymlAdding the EKS cluster to kubeconfig
With AWS CLI, generate the kubeconfig to connect to the cluster:
$ aws --region us-east-1 eks update-kubeconfig --name bottlerocket-clusterBy listing nodes with kubectl command, you can have information on the OS image of the nodes:
$ kubectl get nodes -o=custom-columns=NODE:.metadata.name,ARCH:.status.nodeInfo.architecture,OS-Image:.status.nodeInfo.osImage,OS:.status.nodeInfo.operatingSystem
NODE ARCH OS-Image OS
ip-192-168-18-242.ec2.internal amd64 Bottlerocket OS 1.5.2 (aws-k8s-1.21) linux
ip-192-168-53-240.ec2.internal amd64 Bottlerocket OS 1.5.2 (aws-k8s-1.21) linuxAccessing to Bottlerocket EKS nodes with SSM
List the instances ID with the following AWS command:
$ aws ec2 describe-instances --query 'Reservations[*].Instances[*].[InstanceId]' --output textWith SSM, you can start a session to connect to a Bottlerocket instance:
$ aws ssm start-session --target i-0551208f375cbbec1You can see the current settings with an API request:
$ apiclient get settingsYou can change settings like this:
$ apiclient set motd="hi there" kubernetes.node-labels.environment=testConnecting to Bottlerocket EKS nodes with SSH
Reuse the saved private PEM key used to create the SSH key pair. You'll connect to the admin container:
$ ssh -i ~/.ssh/eks_bottlerocket.pem ec2-user@BottlerocketElasticIPYou can run sheltie command to get a full root shell in the Bottlerocket host. Be careful; while you can inspect and change even more as root.
$ sudo sheltieYou can use logdog through the admin container to obtain an archive of log files from your Bottlerocket host:
# logdogTesting a node group upgrade
$ eksctl upgrade nodegroup --name=bottlerocket-nodegroup --cluster=bottlerocket-cluster --kubernetes-version=1.21Cleaning up the stack
Execute the following commands to clean up the node group and the cluster:
$ eksctl delete nodegroup --cluster bottlerocket-cluster --name bottlerocket-nodegroup
$ eksctl delete cluster --name=bottlerocket-clusterConclusion
Bottlerocket is the result of Amazon's experience and know-how to run containers at scale. It helps to run containers efficiently, enhance better security and ensure operational excellence.
We have seen a quick tutorial with eksctl to explore Bottlerocket on EKS orchestrator. You can also use it with Terraform with this example: